Mr. DNS is a free collection of DNS and network diagnostic tools built for sysadmins, email administrators, and infrastructure teams. The site has been around for years, went offline for a while, and recently relaunched with an expanded tool set. Everything runs in the browser with no account required. If you work with DNS records, mail servers, or IP reputation, there is something here you will use regularly.
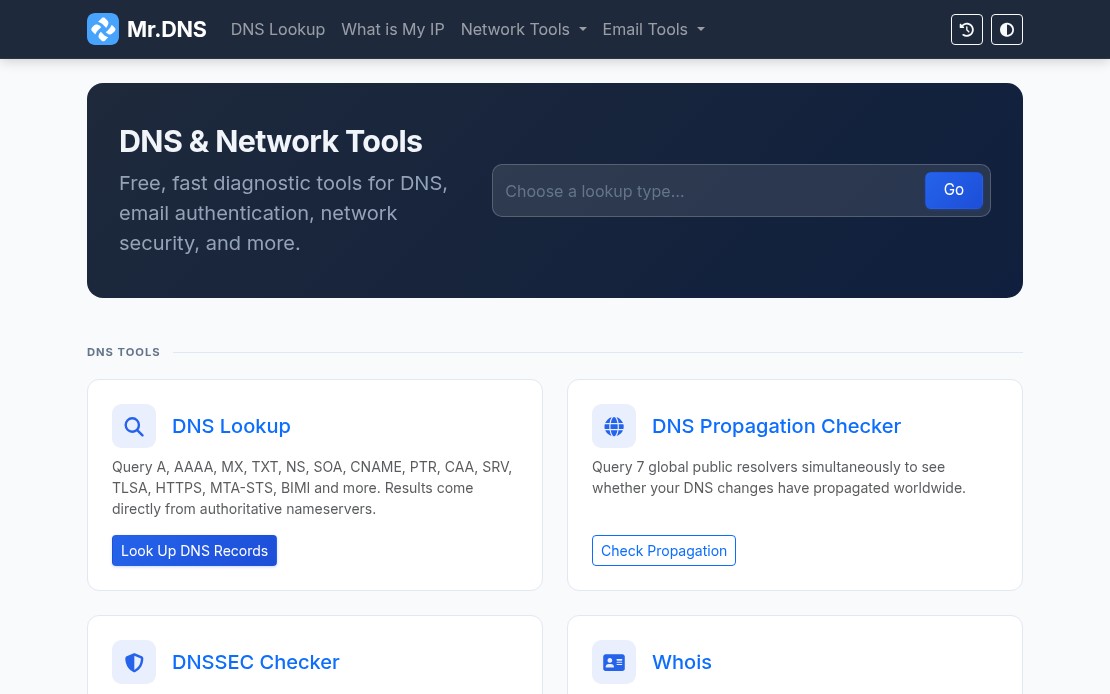
DNS Tools
The DNS lookup tool handles all common record types: A, AAAA, MX, TXT, NS, SOA, CNAME, PTR, CAA, SRV, TLSA, HTTPS, MTA-STS, and BIMI. Results include TTL, geolocation data for nameservers, and flag icons for quick visual scanning.
The DNS propagation checker queries seven global resolvers simultaneously: Cloudflare, Google, Quad9, OpenDNS, AdGuard, NextDNS, and DNS.SB. Useful when you have just made a DNS change and need to see where it has landed without waiting or querying each resolver manually.
The DNSSEC checker validates the full chain of trust: DS records, DNSKEY records, RRSIG presence, and expiry. Good for confirming a DNSSEC deployment before and after changes.
Email Tools
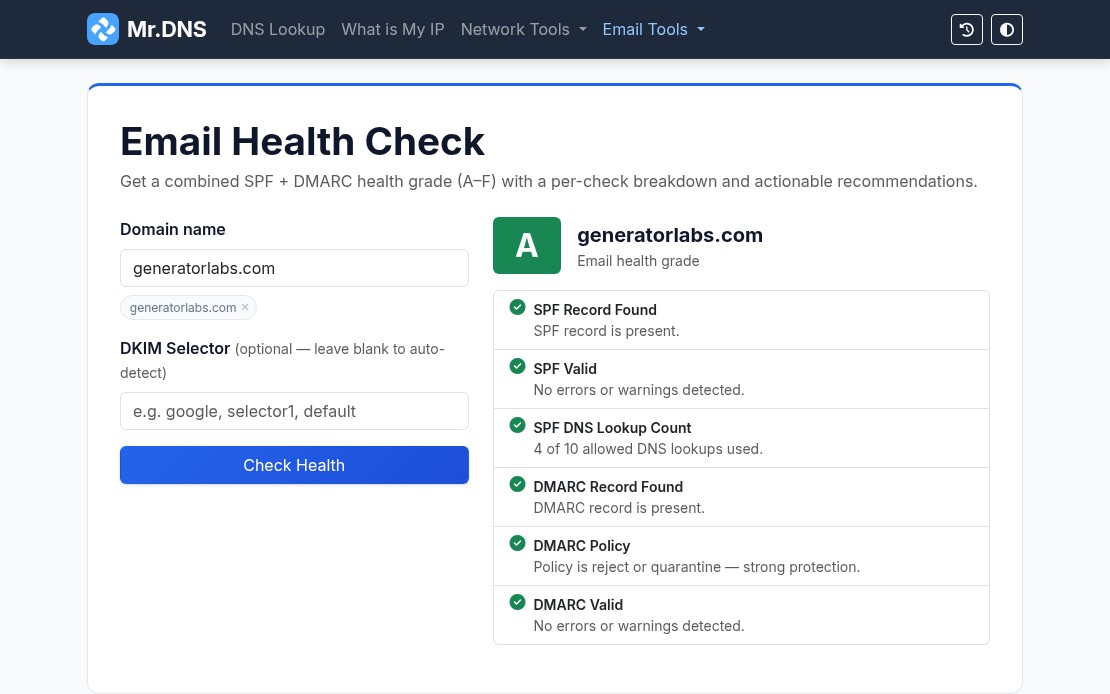
The email tools are where Mr. DNS gets most of its daily use. The email health checker runs a combined SPF and DMARC evaluation and returns a letter grade (A through F) for your domain. One URL, one result, easy to share with a client or manager who needs a status report.
Individual checkers are also available for SPF, DMARC, and DKIM when you need to dig into a specific record. The email header analyzer parses raw RFC 2822 headers and maps the full relay chain with per-hop timing and authentication results, useful for tracing a delivery failure or diagnosing a spam classification issue.
For teams managing outbound mail infrastructure, the MTA-STS checker validates DNS records and policy files, and the BIMI checker verifies SVG logos and VMC certificates for domains using brand indicators in supported mail clients.
Blacklist Checker
The blacklist checker queries your IP or domain against 15+ major RBLs and returns results in seconds. It is a solid first step when a client reports deliverability problems or when you are onboarding a new IP range and want a quick baseline.
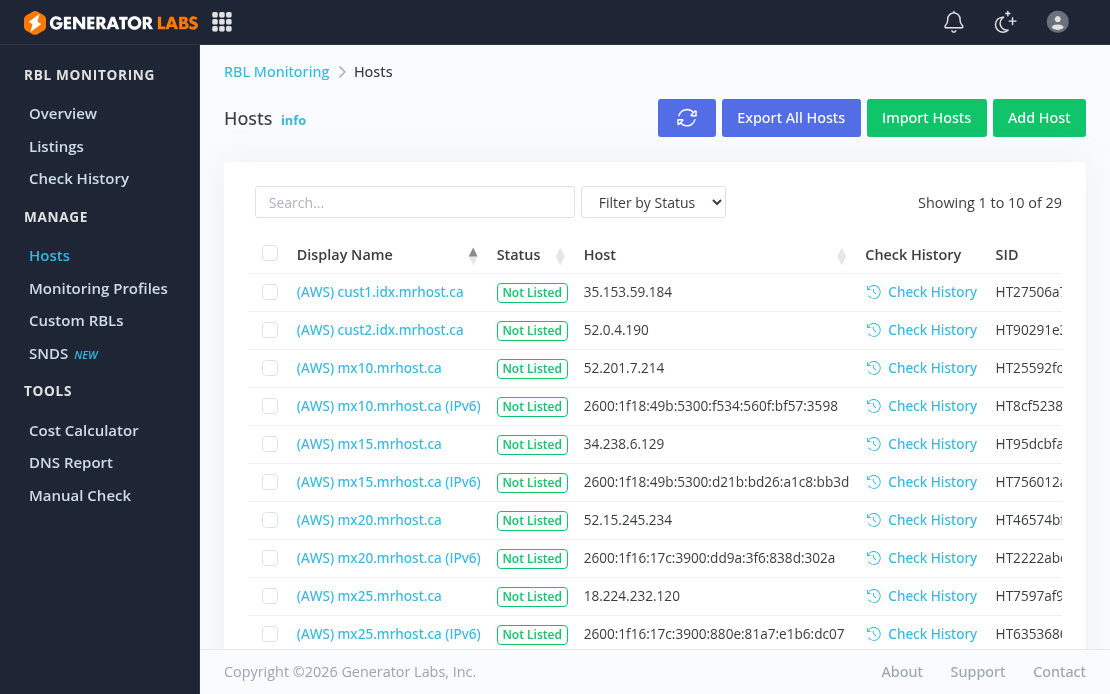
For teams that need ongoing coverage rather than one-off checks, blacklist monitoring from Generator Labs runs continuous checks against hundreds of data sources and sends immediate alerts when a listing is detected. The free tier covers one host with no credit card required.
SSL and Network Tools
The SSL certificate checker inspects certificate details, expiry dates, SANs, issuer chain, and key type for any domain. Useful for a quick manual check before or after a certificate renewal.
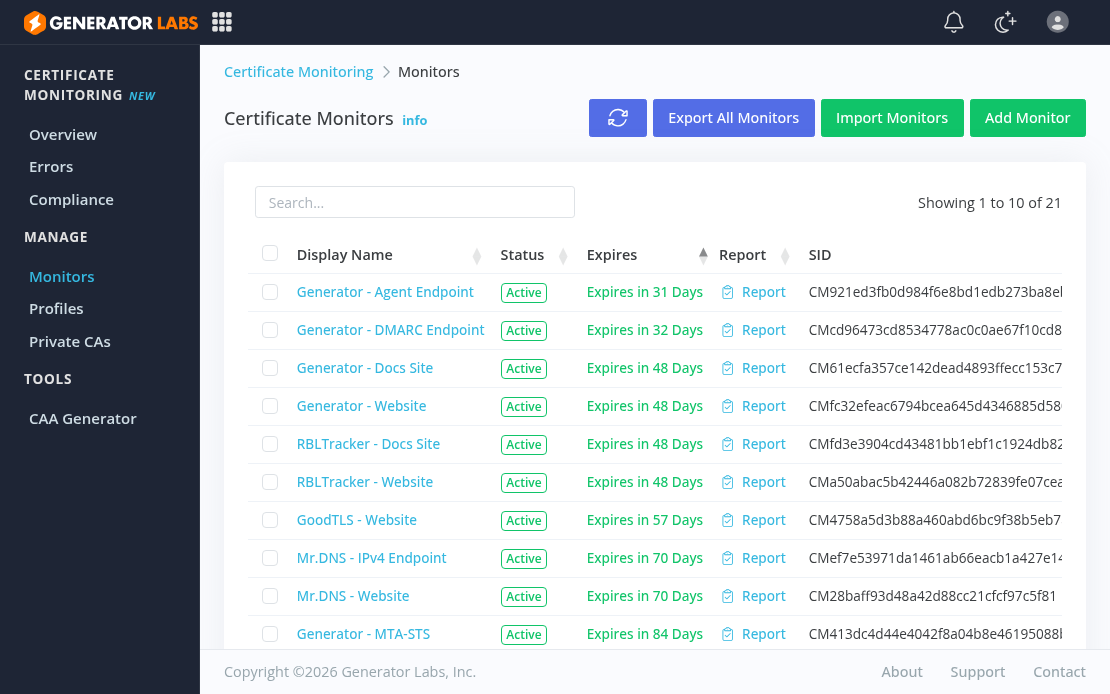
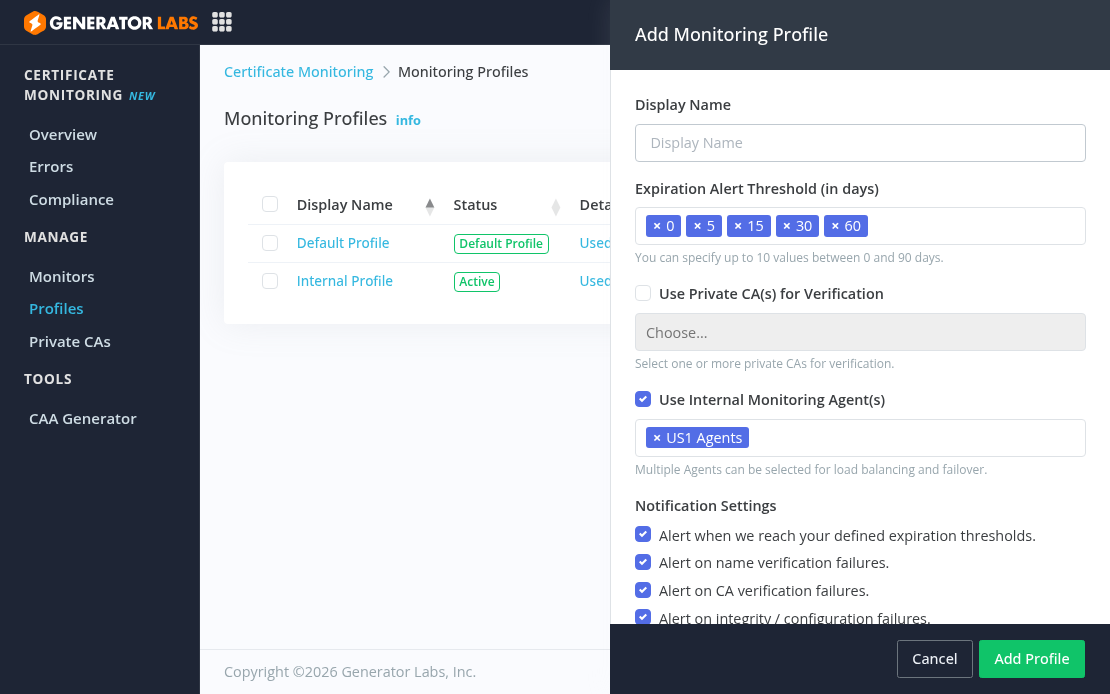
For automated tracking across many domains, certificate monitoring from Generator Labs handles the ongoing work: scheduled checks, configurable expiry alert thresholds, and multi-channel notifications before anything expires.
Other network tools include ping, traceroute, port checker, HTTP headers inspector, HTTP/2 and HTTP/3 checker, and a what is my IP tool that detects both IPv4 and IPv6 with geolocation and ASN data.
Generators
Mr. DNS includes generators for SPF records and DMARC records for teams setting up email authentication from scratch. Both walk through the options and output a ready-to-paste DNS record.
Bottom Line
Mr. DNS covers the diagnostic side of DNS and email infrastructure without requiring an account or payment. For the monitoring side, Generator Labs provides continuous blacklist monitoring and certificate monitoring with alerting, picking up where the one-shot tools leave off. Both are worth bookmarking if you manage any kind of mail or DNS infrastructure.